Tor and VPN both provide privacy protection but in different ways. So should we combine the privacy and security features of each tool together? This is a question that many people are interested in. Let's find the answer with WebTech360!

Are Tor and VPN the same?
The first thing to consider is the difference between Tor and a VPN. Fundamentally, Tor and VPN are not the same.
- Tor is an anonymous communication network that routes Internet traffic through a global network of nodes, protecting data in the Tor Browser and Tor Network.
- VPN encrypts the network connection, tunneling all data through the VPN provider's server. Internet traffic will appear to come from the VPN server's IP address, instead of your physical location.
Tor and Tor Browser
When using Tor, you connect to the Tor Network using Tor Browser (a modified version of Mozilla Firefox). Every activity in the Tor Browser uses the Tor Network for protection, with each traffic node maintaining network encryption.
Tor Network does not protect Internet activity that occurs outside of Tor Browser. So, if you complete your search in a regular browser, you don't have the same multi-layered security and privacy in Tor Browser.
Tor Browser and Tor Network provide extensive protection in that environment, even the Dark Web. Many people use Tor Browser for specific tasks to access certain content, rather than just relying on their everyday Internet browser.
VPN
VPNs, on the other hand, encrypt the entire Internet connection, routing it through the VPN provider's servers. VPNs differ from Tor in that all Internet activity is protected, not just activity within the Tor Browser.
You can use a VPN all day, every day to increase your privacy and security online. However, a fatal misconception here is that VPNs provide complete privacy. That's not right. If you log into an online account while using a VPN, the service will still know you are logged in. The only difference is that this service sees network traffic coming from an unusual location.
Additionally, if you use a free VPN service, there is no guarantee that the provider will not log your data or will pass your information on to the authorities.
Should I use a VPN with Tor Browser?
Tor's official manual page states that you do not need to use a VPN with Tor for increased security. Configure Tor Network securely. Although the threat of malicious exit and entry nodes still exists, it does not cause you any harm.
That is the official information on the homepage. However, using a VPN with Tor has a slight impact on your connection.
Tor Over VPN
If connecting to a VPN provider before Tor Network, the entry node will receive the IP address of the VPN service that is the source of the data, replacing your actual IP address. The provider will not see that you are connecting to Tor. This can protect your privacy, even allowing you to access the service in some countries.
This method is called Tor Over VPN. It has some warnings regarding the VPN provider. If you trust the VPN provider to be completely log-free and within a safe jurisdiction, you can use this method.
If not, you can simply transfer your trust from your network provider to a VPN. If your VPN provider logs data and works with authorities, you should use Tor, no need for a VPN.
Tor Over VPN also provides security against malicious entry nodes. This is another plus.
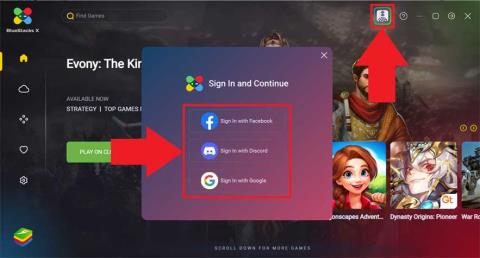
If you're considering using Tor Over VPN, you should sign up for an ExpressVPN subscription. It has always been one of the best VPN providers.
VPN Over Tor
The Over Tor VPN method is a bit different. When using this method, first you need to open Tor Browser and connect to Tor Network. Then, connect to the VPN provider via Tor Network.
The main benefit of VPN Over Tor is to help you access sites that do not allow connections from known Tor exit nodes. VPN Over Tor also protects you against malicious exit nodes. This is a great advantage.
VPN Over Tor is considered more difficult to use because you have to configure the VPN to use it over Tor. However, it can provide greater anonymity, protecting your access as it goes through the exit node and back to the VPN provider's server. However, this also makes Tor increasingly difficult to use.
Some users evaluate that VPN Over Tor does not increase security or privacy enough to meet their usage needs, especially when it takes time to configure the VPN to use Tor. Furthermore, if operated incorrectly, it can expose your data.
Tor Bridge
Tor Project recommends using bridge relay (bridge for short) to increase the privacy of node entry. A Tor bridge is an entry node that is not listed. If you suspect a provider or someone else is monitoring connections to the Tor Network via a regular entry node, you can use a bridge relay to connect an unmonitored relay and securely enter the Tor Network.
Here is a list of default Tor bridges that anyone can use. However, because it is all public, most of it can be monitored.
In general, you can use a VPN with Tor securely using Tor Over VPN. For most people, this extra layer of privacy is overkill. It's important to remember that you should use a VPN that keeps no logs and is trustworthy.