What is WiFi? How does WiFi work?

WiFi is a form of local area networking and wireless Internet access used by people around the world to connect their devices to the Internet without cables.
While Wi-Fi security is more advanced in 2025, it's not perfect. The following threats continue to emerge, so think twice before browsing on an unknown connection.
1. Old Wi-Fi protocols still exist
Many people still use public Wi-Fi networks normally to send emails and watch videos, seemingly oblivious to the potential risks.
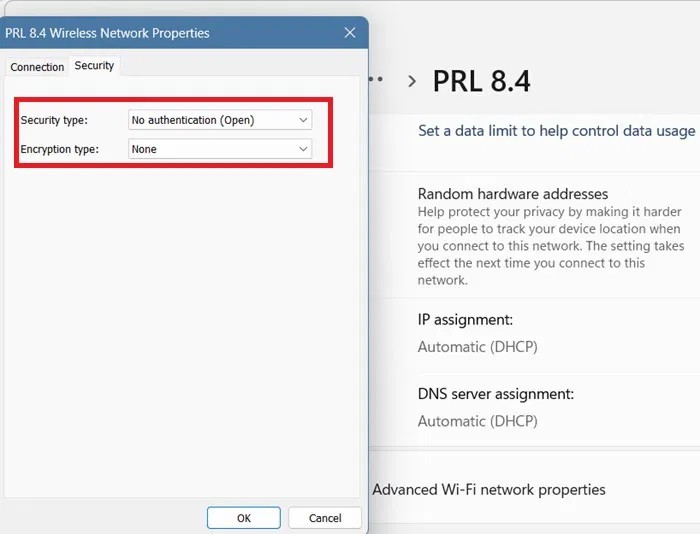
In addition to open Wi-Fi networks, you can still find older protocols like WEP and WPA. If you're in a hurry, you might connect to these networks without verifying their integrity. These older networks have weak encryption and are vulnerable to hacking and session hijacking tools.
To help you stay safe, here are a few different methods for checking your Wi-Fi network's encryption on Windows, Android, iOS, and Mac—especially useful if you're traveling internationally or living as a digital nomad .
2. Lack of Forward Secrecy – A Challenge with WPA2
The biggest challenge with WPA2-AES or WPA2-TKIP is the lack of forward secrecy. Public Wi-Fi networks continue to use simple passwords that are shared with everyone. Anyone with access to this key can decrypt all past or future sessions on the network.
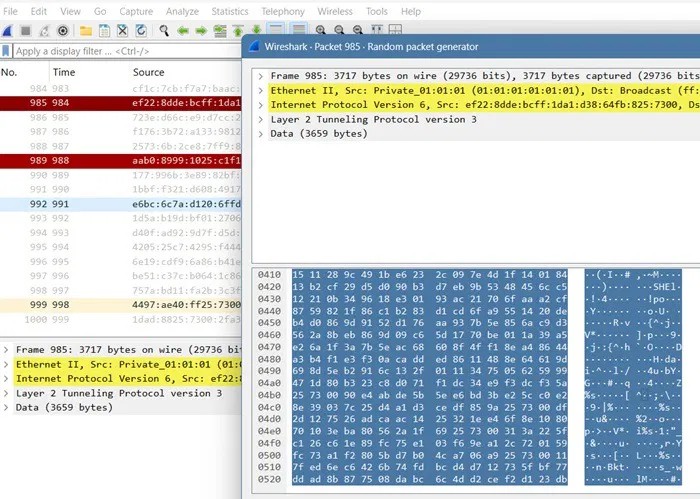
Penetration tools like Wireshark provide a glimpse into captured SSL/TLS traffic. If someone has access to the server key, they can decrypt all the data. This can potentially expose login credentials, emails, etc., so using a VPN is important on public Wi-Fi networks as it encrypts all your data transmissions.
WPA3 is the gold standard for Wi-Fi security, providing strong protection against the above attacks. It uses Simultaneous Authentication of Equals (SAE), which encrypts each user session separately. You may have encountered this at airports, where a unique session key is generated after you share your passport number.
While WPA3 is highly secure, unfortunately it will take a few more years before it is widely used in public places.
3. The real problem of fake hotspots
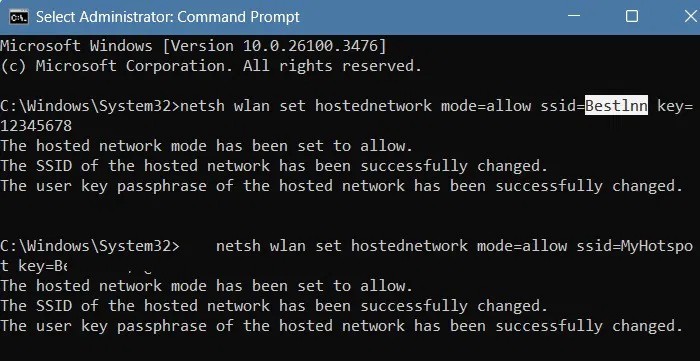
As many frequent travelers have begun to notice, fake hotspots are becoming a big problem in hotels and other public places. Essentially, anyone can create a fake SSID to mimic the original SSID provided by your location.
All the crooks have to do is enter a set of commands that look similar to the original Wi-Fi hotspot. For example, instead of a hotel name like “Best Inn,” the “I” might be replaced with a lowercase “L.” Hackers even copy captured portals and logos to give it an authentic look.
Again, the best way to spot a fake hotspot is to check the Wi-Fi encryption protocol it uses. Of course, they won’t use WPA3 to protect your session. If there are multiple hotspots with the same name, you’ll need to use a VPN or one of the alternatives.
4. Beware of hijacked browser sessions
Most websites today use HTTPS , but that doesn't mean all information is safe from hackers. HTTPS protects the content of your communication, but not the metadata.
If you’re using a public Wi-Fi network on secure WPA3, you’d think all the security holes would have been patched. But hijacking can attack your device on a public network – even if you’re on a very secure connection. Session hijacking involves hackers taking over your browsing data through account takeover (ATO) attacks or malware, which can originate on the dark web .
The human factor is one of the biggest reasons behind these attacks. Your identity is at the heart of device security. On Android, you can use Identity Check to prevent your device from being taken over. Similarly, iOS, Windows, and Mac devices also use biometric authentication to prevent your accounts from being taken over.
Safety precautions when using public Wi-Fi
While the risks of public Wi-Fi have decreased significantly compared to a few years ago, they are still very common in 2025. However, you can still use public Wi-Fi, as long as you remember to keep the following safety precautions in mind:
WiFi is a form of local area networking and wireless Internet access used by people around the world to connect their devices to the Internet without cables.
To make your mobile hotspot stand out and be easier to find, you can give it a unique and distinctive name.
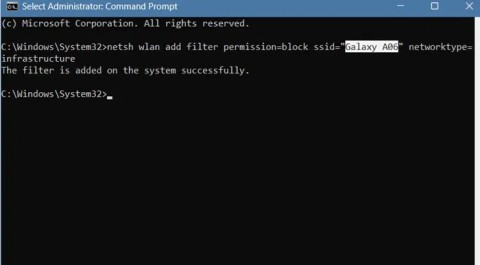
You can completely hide a Wi-Fi network or prevent it from showing up again. You can also block all other Wi-Fi networks, allowing your computer to only show and connect to the Wi-Fi networks you want easily.
To ensure better security, devices running Android 10 and above will use random WiFi MAC addresses by default.
When you want to connect to wifi in a public place, you will find some wifi networks with the word Guest, this is the guest network, also known as the Guest Network. In this article, we will learn more about the guest network as well as how to set up this network for the Router.
Most Wi-Fi routers today want to apply Beamforming technology to improve Wi-Fi transceiver capabilities, avoid interference, and increase connection speed for terminals. So what is Beamforming, how does it work? This article will introduce you to the Beamforming technology.
Since 2015, the MU-MIMO concept appeared with the promise of a technology that speeds up to 4x faster than traditional routers. The following article will help you better understand MU-MIMO technology.
When you use the network, especially the Wifi network, the slow and losing network phenomenon is unavoidable, there are many causes of this unpleasant phenomenon, possibly due to the network operator, the connection line. unstable connection, user download overload, and
Long-distance travel can involve heavy traffic, changing weather conditions, and rider fatigue. If you are also dealing with the responsibilities of moving home, such as packing belongings or coordinating accommodation, a long ride may add unnecessary pressure to an already busy schedule.
Tired of Microsoft Teams shortcut error preventing you from opening the app? Follow our expert, step-by-step guide with the latest fixes for instant resolution. Works on Windows, Mac & web – no tech skills needed!
Tired of Microsoft Teams Task Management Sync Error halting your workflow? Follow our proven, step-by-step fixes to resolve sync issues fast and restore seamless task collaboration. No tech expertise needed!
Struggling with Microsoft Teams Wiki Error Formatting? This step-by-step guide reveals proven fixes for common wiki tab issues, ensuring smooth editing and collaboration in Teams. Get back to productive wikis fast!
Struggling with Microsoft Teams installation error on Linux? Discover step-by-step fixes for Ubuntu, Fedora & more. Resolve dependency issues, crashes, and errors quickly with our ultimate guide. Get Teams running smoothly today!
Struggling with Microsoft Teams "Error Page" not loading? Get step-by-step fixes for desktop, web, and mobile. Solve Microsoft Teams Error Page issues quickly and resume seamless teamwork today.
Tired of Microsoft Teams "Error Screenshot" blocking your workflow? Get proven, step-by-step solutions to resolve screenshot errors in Teams instantly and boost productivity. No tech skills needed!
Tired of Microsoft Teams "Error U" User blocking your chats? Get proven, step-by-step fixes to clear cache, reset, and restore seamless collaboration instantly.
Unlock the precise locations of Microsoft Teams registry keys on Windows 11. Step-by-step guide to find, access, and safely tweak them for optimal performance and troubleshooting. Essential for IT pros and Teams enthusiasts.
Tired of Microsoft Teams "Training Error" Video Lag ruining your meetings? Follow our step-by-step guide with the latest fixes for smooth video calls—no more frustration!
Frustrated by Microsoft Teams "Error occurred" during sign-in? Discover proven, step-by-step fixes to get back online fast. Clear cache, reset app, and more for seamless login. Works on Windows, Mac & web.
Struggling with Microsoft Teams "Call Error" Disconnecting? Discover proven, step-by-step fixes for call drops, network issues, and more. Get back to seamless meetings fast with our expert troubleshooting guide.
Stuck in Microsoft Teams Error 2603 login loop? Get proven step-by-step fixes to resolve the issue fast and restore seamless teamwork. Clear cache, reset, reinstall – all covered!
Tired of Microsoft Teams voice call errors? Follow our step-by-step guide to troubleshoot no audio, echo, or call drops. Proven fixes for crystal-clear calls every time.
Struggling with Microsoft Teams "Workflows Error" in Power Automate? Discover proven, step-by-step fixes to resolve connection issues, permissions, and more. Get your workflows running smoothly today!